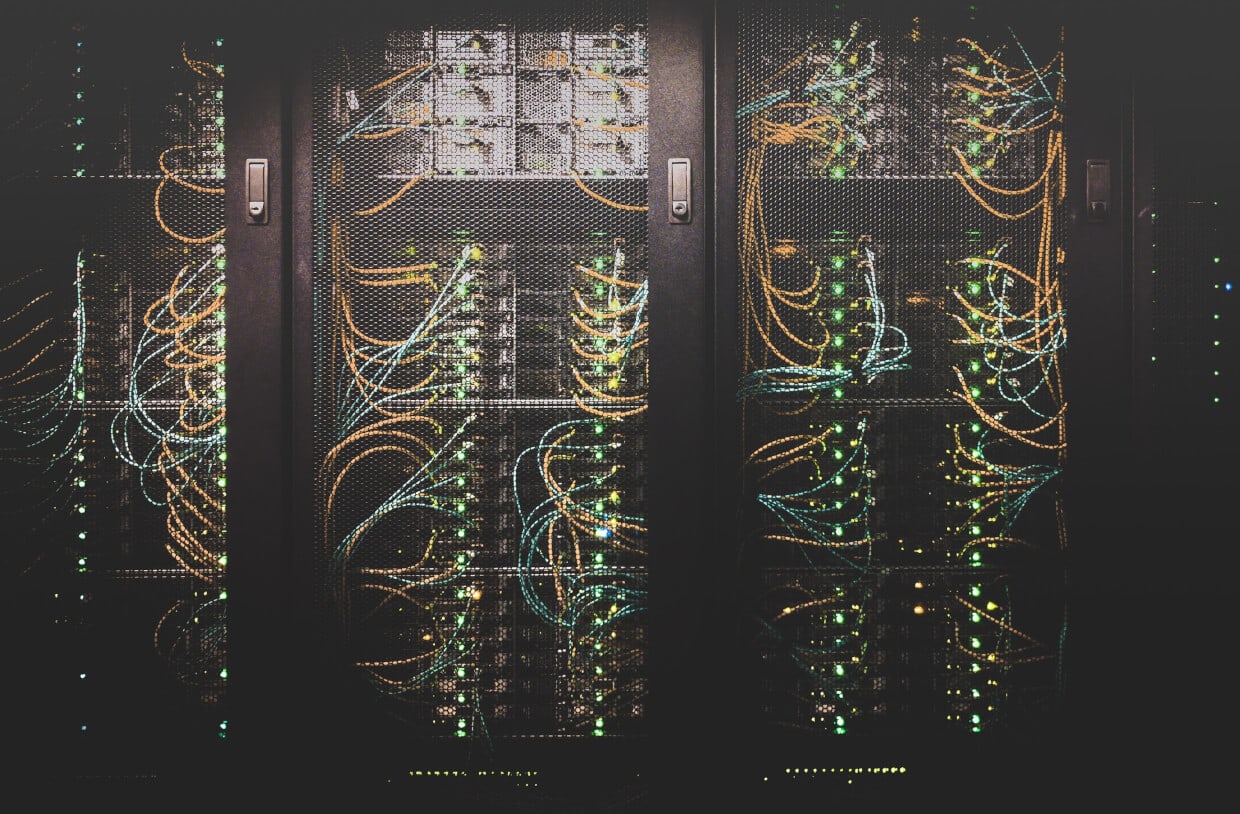
What Is Data Center Security? 6 Ways to Ensure Your Interests Are Protected - Hashed Out by The SSL Store™

Should Data Centers Have Common Infrastructure Security Standards? | Data Center Knowledge | News and analysis for the data center industry

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

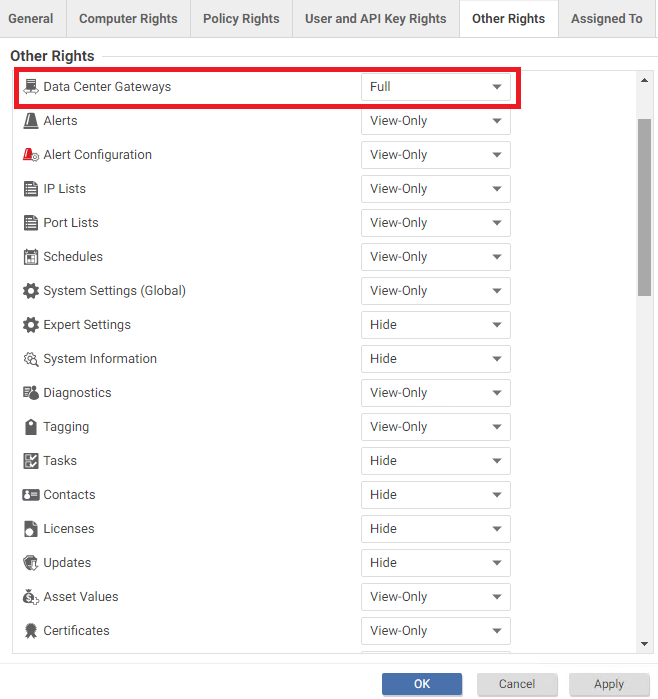
The Reasons You Should Integrate IAM With Data Center Security | Unleash Your Productivity – Unleash Blog

The Reasons You Should Integrate IAM With Data Center Security | Unleash Your Productivity – Unleash Blog

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls | AWS Big Data Blog

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls | AWS Big Data Blog

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls | AWS Big Data Blog