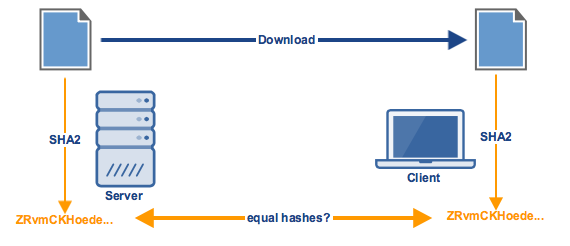
Using a Digital Signature to Validate Data Integrity Figure 2 shows two... | Download Scientific Diagram

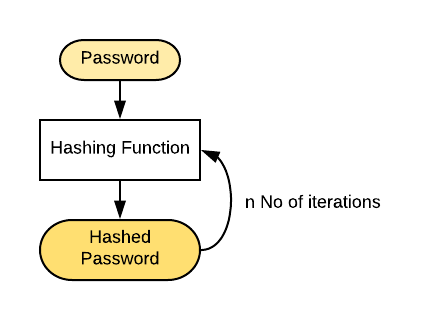
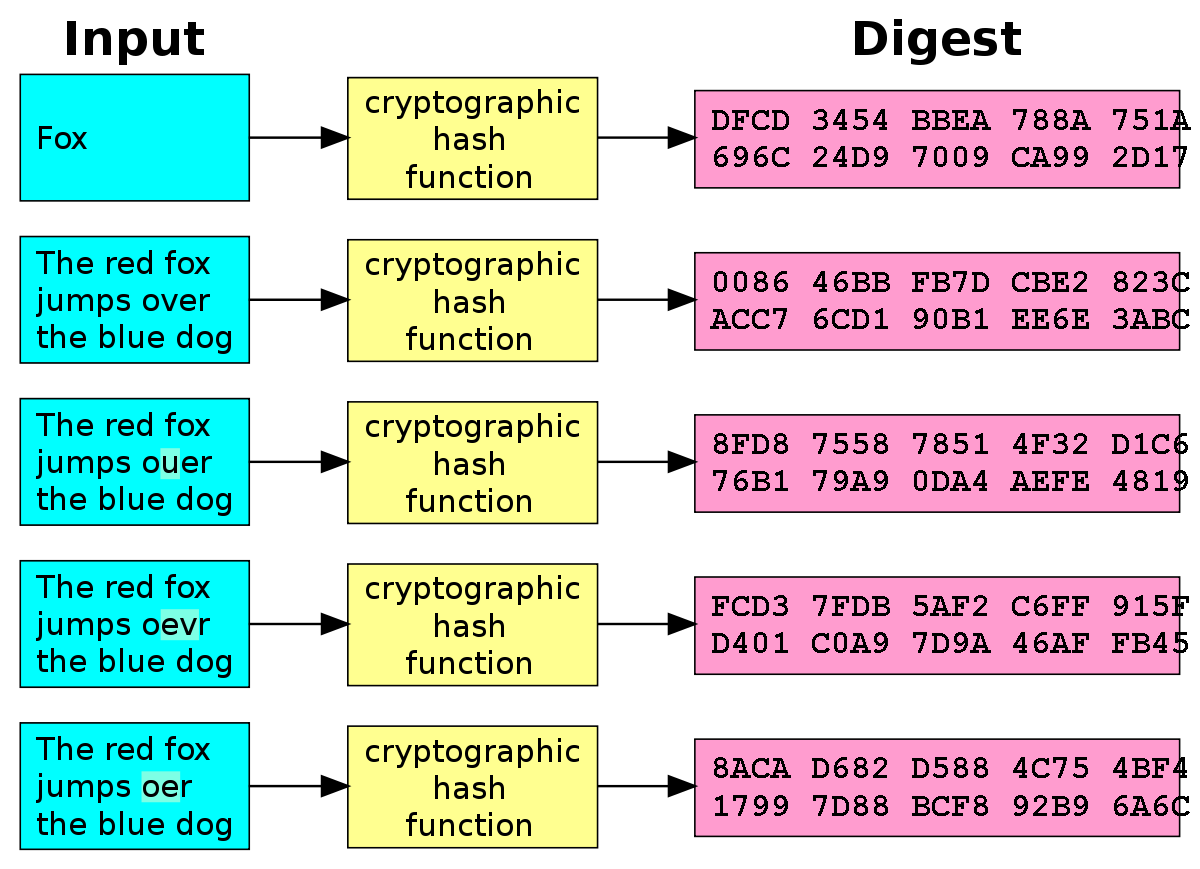
Hash Functions A hash function H accepts a variable-length block of data M as input and produces a fixed-size hash value h = H(M) Principal object is. - ppt download

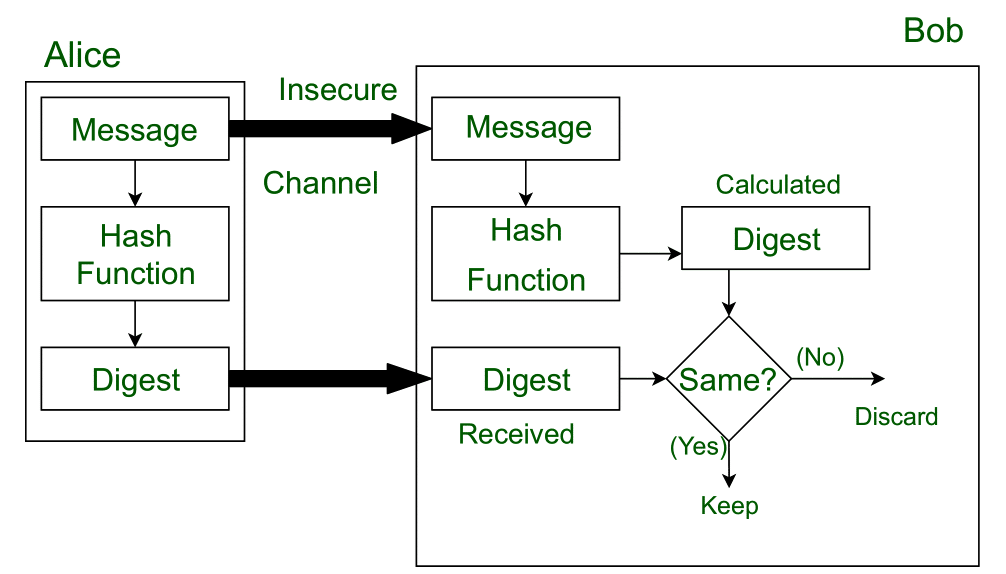
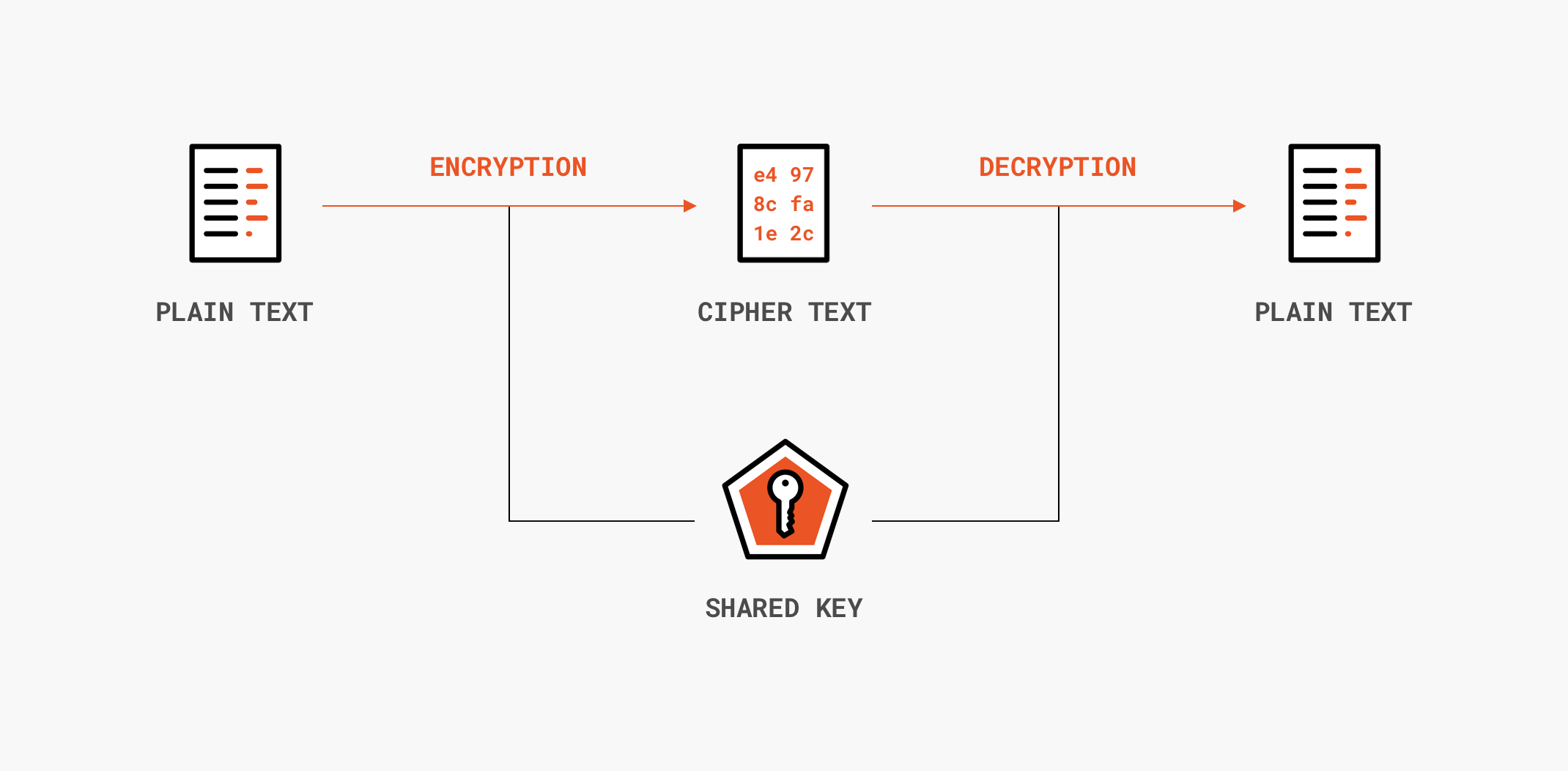
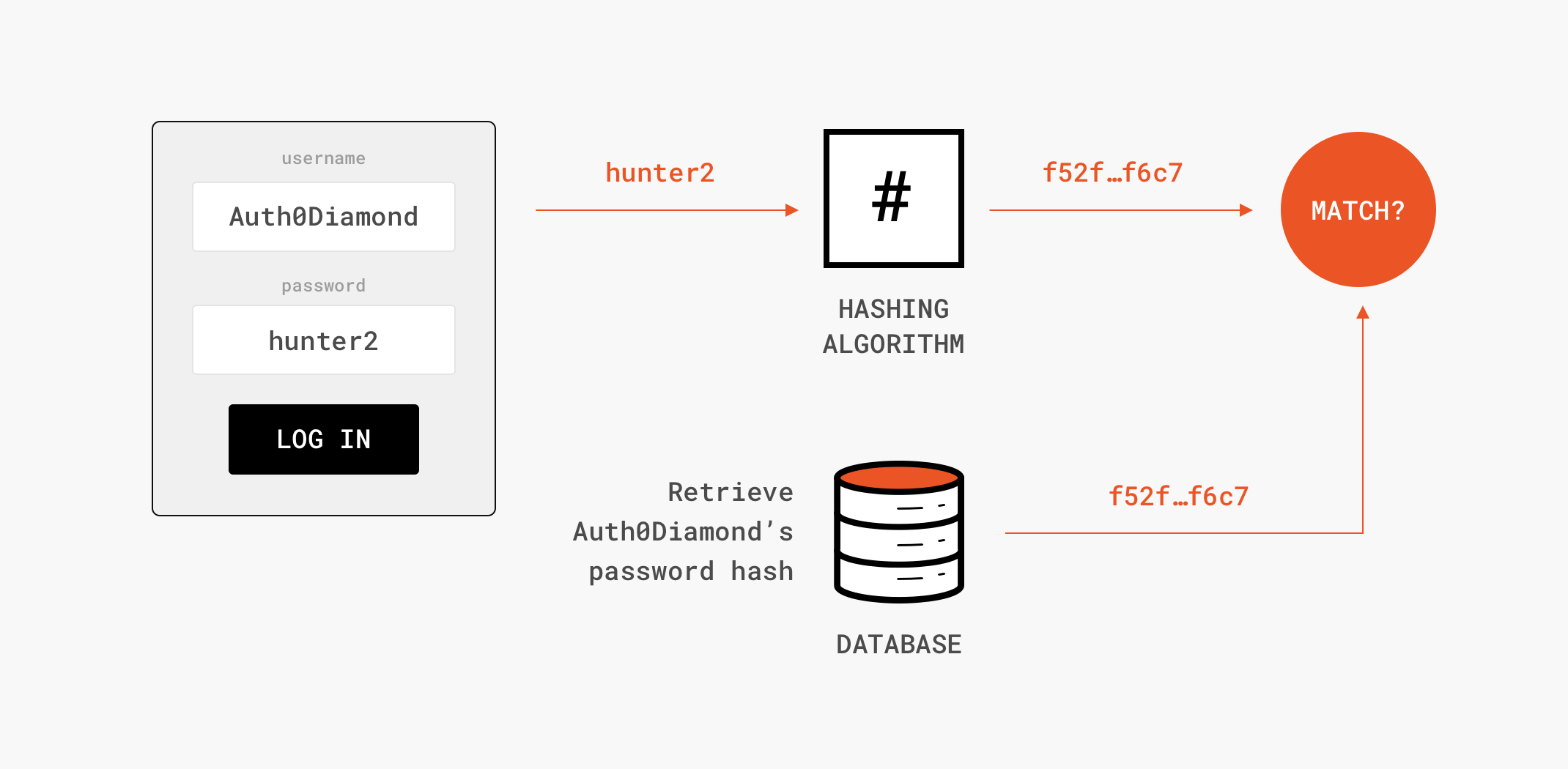
Ensuring integrity, authenticity, and non-repudiation in data transmission using node.js | by Glauber | GeeKoffee | Medium